For UAE CFOs, upgrading from legacy VPNs to Zero Trust is a critical strategic move. Beyond IT, it enhances risk management, boosts productivity, controls costs, and ensures scalability, making it essential for modern businesses.
From a CFO's perspective, replacing a legacy VPN is not merely an IT modernization exercise. It is a strategic decision that sits at the intersection of enterprise risk management, productivity enablement, cost control, governance, and scalability.
For many businesses, VPNs were introduced as a practical solution for remote access. At the time, they served a purpose. However, the operating environment has changed materially. Today's organizations are working across hybrid teams, cloud applications, third-party vendors, remote employees, and geographically distributed operations. In that environment, a legacy VPN model can create wider access than necessary and expose the business to inefficiencies and avoidable risk.
VPNs Are No Longer Just a Technical Matter A traditional VPN typically grants a user entry into the wider corporate network once the first authentication step is completed. In practical terms, this often means the user gets broader access than the business truly intends. For a finance leader, that should immediately raise concerns around internal controls, access discipline, audit readiness, and risk containment.
This is where Zero Trust Network Access, or ZTNA, becomes commercially relevant. Rather than assuming trust after initial connection, Zero Trust validates every access request based on identity, device posture, and context. In simple terms, it is a more disciplined and targeted way of controlling who gets access to what. That shift is important because it changes not only the control framework, but also the economics of access and the resilience of the business.
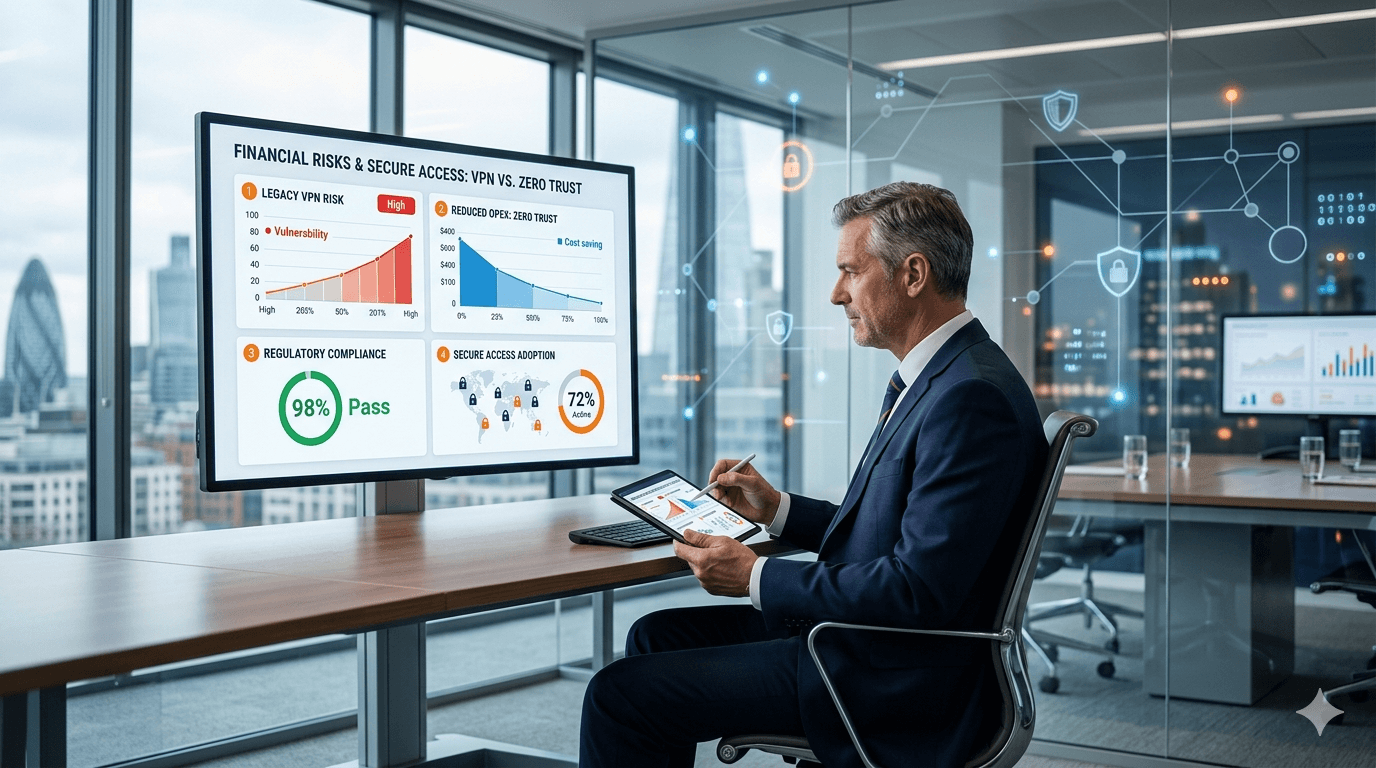
1. Risk Reduction Has a Direct Financial BenefitThe first priority for any CFO is risk. Legacy VPN models can result in overly permissive access. If credentials are compromised, the attacker may gain broader movement inside the environment than intended. The financial implications of that can be severe: regulatory exposure, remediation costs, business interruption, reputational damage, customer trust erosion, and management distraction.
A Zero Trust approach strengthens the control environment by verifying the user, the device, and the context before granting access. For finance leadership, that means stronger governance, greater audit defensibility, and a more robust approach to protecting enterprise value.
2. Legacy VPNs Create Hidden Operational CostsMany businesses underestimate the true cost of running legacy access infrastructure. The visible cost may be limited to software, support contracts, or appliances. The hidden cost is far broader: manual provisioning, access changes, helpdesk tickets, password-related issues, onboarding and offboarding delays, and IT troubleshooting effort. These costs rarely sit neatly in one line item, yet they consume management time, skilled resources, and organizational capacity.
A modern Zero Trust model can simplify setup, centralize policy administration, support clientless access for web applications, and improve automation. From a financial advisory standpoint, that is not simply a technology enhancement; it is an operating model improvement that can reduce cost-to-serve and improve internal efficiency.
3. User Experience Affects Productivity and ThroughputProductivity is often overlooked in access architecture discussions, yet it has measurable commercial impact.
When employees, consultants, or contractors face slow, unreliable, or cumbersome remote access, that friction reduces output and responsiveness. It affects turnaround time, staff experience, and execution speed. Even a small inefficiency, when multiplied across a large workforce over time, becomes a significant hidden productivity tax.
A more modern access model can improve speed, reduce friction, and support a smoother user experience. For finance leaders, that translates into better workforce throughput and stronger operational agility.
4. Delaying Action Also Carries a CostA common budgeting mistake is to assume that keeping legacy infrastructure is the lower-cost option simply because it already exists.
In reality, delay carries its own financial burden. The underlying brief identifies financial costs such as rising bandwidth and hardware expenses, operational costs such as slower onboarding and delayed rollout of applications, and security costs linked to breaches, slow incident response, and compliance pressure.
From a financial advisor's perspective, this is critical. Legacy environments often appear economical only because their true cost is fragmented across infrastructure, support, risk, downtime, and lost productivity. Over time, that fragmentation can make the status quo more expensive than modernization.
5. Access Architecture Now Supports Business AgilityModern businesses need secure and flexible operating models.
They need to onboard contractors quickly, enable third-party access safely, support developers without creating bottlenecks, and automate joiner-mover-leaver processes. These are no longer niche technical concerns. They are operational capabilities that affect growth, outsourcing, restructuring, and integration readiness.
For CFOs, that means access architecture should be viewed as part of the broader business enablement agenda. A stronger model supports scale, preserves control, and reduces operational friction during periods of change.
6. A Phased Transition Makes Commercial SenseOne of the strongest aspects of a Zero Trust transition is that it does not need to be approached as a disruptive, all-at-once program.
A business can begin with a focused pilot covering critical applications or higher-risk user groups. It can test value early, measure the outcome, and then scale the model gradually. This phased approach supports controlled investment, measurable milestones, proof of value, and tighter alignment between spending and business benefit.
From a finance standpoint, that is the right way to govern the initiative. It converts what might otherwise feel like a broad IT transformation into a disciplined commercial decision backed by evidence and milestones.
What Finance Leaders Should Be Asking A CFO does not need to become a network engineer to lead this discussion effectively. The right role is to ask commercially relevant questions such as:
What business risk are we reducing? What is the true total cost of the current access model? Where are the biggest inefficiencies today? Which users and applications should be prioritized first? What costs sit outside the software license? How will success be measured during the pilot? What is the three-year total cost of ownership? How does this improve our control and compliance posture?
These are the questions that elevate the conversation from technical preference to strategic value creation.
Conclusion The business case for replacing a legacy VPN is no longer limited to cybersecurity. It is about creating a stronger, leaner, and more scalable operating model.
For CFOs and financial advisors, the issue should be assessed across four commercial dimensions: risk reduction, operating efficiency, productivity improvement, and long-term scalability. A Zero Trust approach is increasingly aligned with modern business realities because it improves control, reduces hidden cost, enhances user experience, and supports disciplined modernization.
In a market where resilience, agility, and governance are critical, the real question is not whether the legacy VPN still functions. The real question is whether it remains economically and strategically fit for purpose.
If your business is still relying on a legacy VPN environment, this is the time to assess the issue through a financial and strategic lens, not merely a technical one.
The right question is not, "Can our current system still operate?" The right question is, "What is the hidden cost of maintaining it, and what risk is the business continuing to carry?"
At Bridgewater Management Consultancies, we help business owners, CFOs, and leadership teams evaluate operational and control frameworks from a commercial perspective. That includes identifying hidden cost drivers, assessing risk exposure, improving process efficiency, and supporting better investment decisions as businesses scale.
If you want an independent, business-focused review of whether your current access model is still fit for purpose, let us help you evaluate it in practical financial terms.
Speak to us for a strategic review of your current operating and control environment.
Mahesh Thadani Bridgewater Management Consultancies Email: sales@bwmc.ae Website: www.bwmc.ae Mobile / WhatsApp: +971 528766284
Written By

Written by
Mahesh Thadani
Director
Mahesh Thadani is a seasoned Certified Chartered Accountant and senior finance professional with extensive expertise across taxation, financial advisory, and international business structuring. With a strong command over UAE regulatory frameworks—including VAT, Corporate Tax, ESR, AML, and KYC compliance—he advises businesses on navigating complex financial and legal landscapes with precision and strategic clarity.